Understanding the Itron Cyberattack: Impacts and Lessons [2025]
The cyberattack on Itron, a major player in utility technology, has sent ripples through the industry. While the company reported that their internal systems were accessed, they confirmed that data was not tampered with and no material disruption occurred. This incident serves as a crucial reminder of the vulnerabilities in utility infrastructures and the importance of robust cybersecurity measures.
TL; DR
- Itron experienced a cyberattack, affecting internal systems but causing no significant disruption, as detailed in SecurityWeek's report.
- Sensitive data was not compromised, according to the company's preliminary reports, as noted in StockTitan's filing.
- Cybersecurity response plans were activated promptly to block the intrusion and mitigate risks, as highlighted by InfoSecurity Magazine.
- Lessons from this incident underscore the need for enhanced security protocols in utility sectors.
- Future trends indicate increased investment in AI-powered security solutions, as projected by Fortune Business Insights.

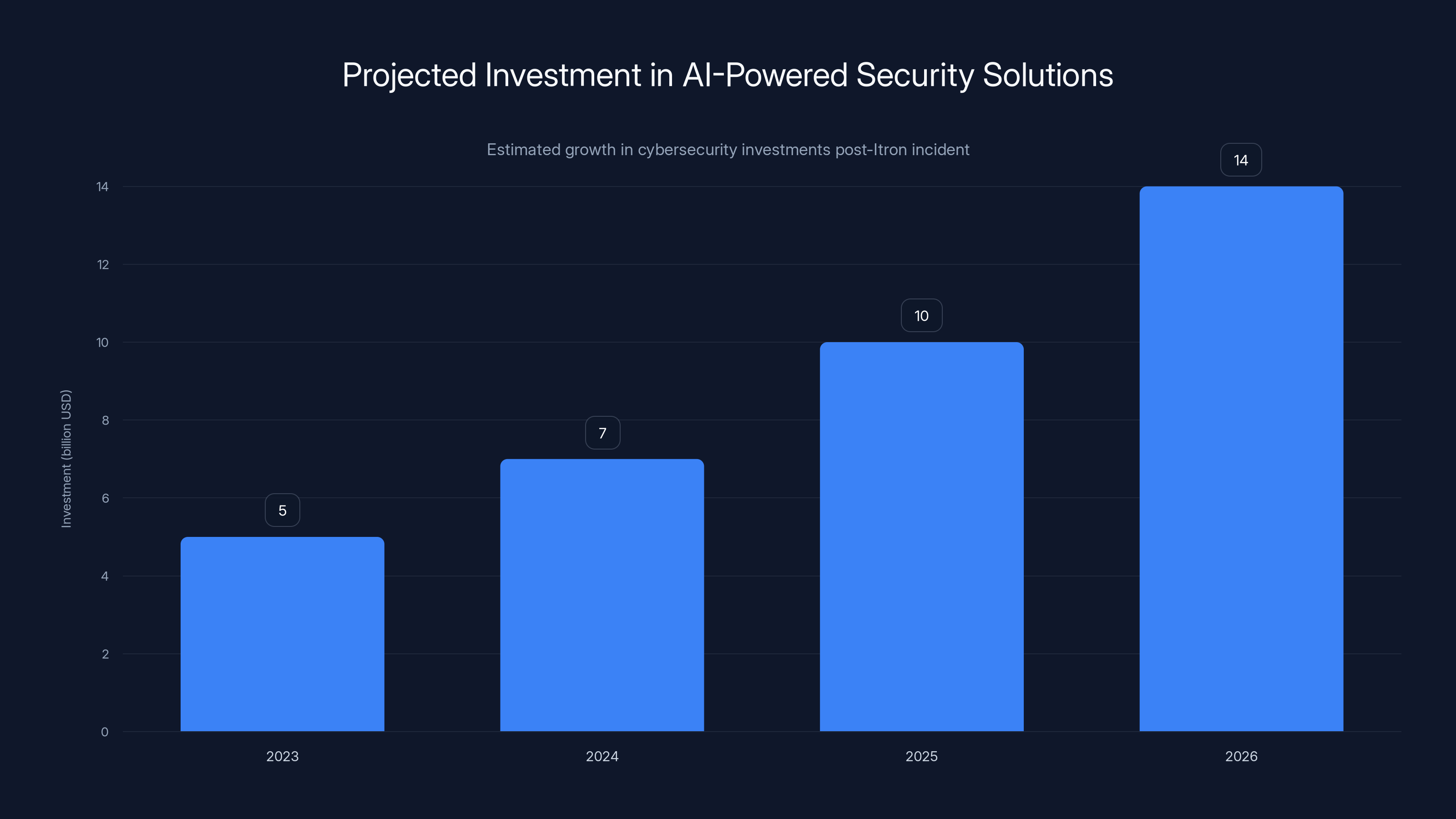
Estimated data suggests a significant increase in AI-powered security investments in the coming years, driven by incidents like the Itron cyberattack.
The Itron Cyberattack: An Overview
On [DATE], Itron, a utility technology giant, confirmed that it had been the target of a cyberattack. While the specifics of the breach have not been fully disclosed, initial reports suggest that hackers accessed internal systems but did not manage to tamper with or extract sensitive data, as reported by TechRadar. The company's quick response and activation of its cybersecurity plan were pivotal in containing the threat.
The Nature of the Attack
Cyberattacks on utility companies are particularly concerning due to the potential for widespread disruption. While Itron managed to avert a major crisis, the attack highlights the vulnerabilities inherent in the digital infrastructure of utility providers. Such attacks can range from ransomware attempting to encrypt critical systems to more insidious intrusions aimed at stealing data or disrupting operations, as discussed by CSIS.
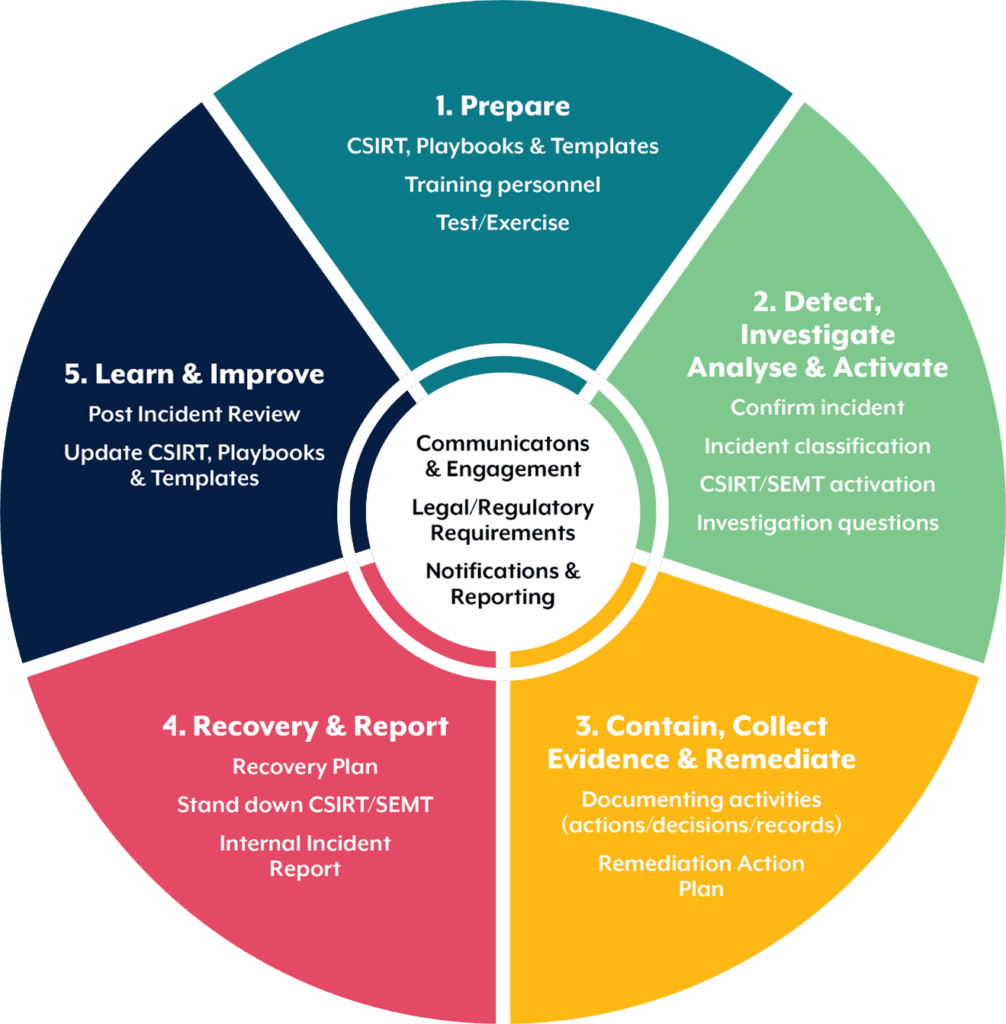
Response and Mitigation
Itron's response to the attack was swift. The company activated its cybersecurity response plan, which included isolating affected systems, conducting a forensic investigation, and enhancing security measures to prevent future intrusions. This incident underscores the importance of having a well-defined response strategy in place, as emphasized by SC World.

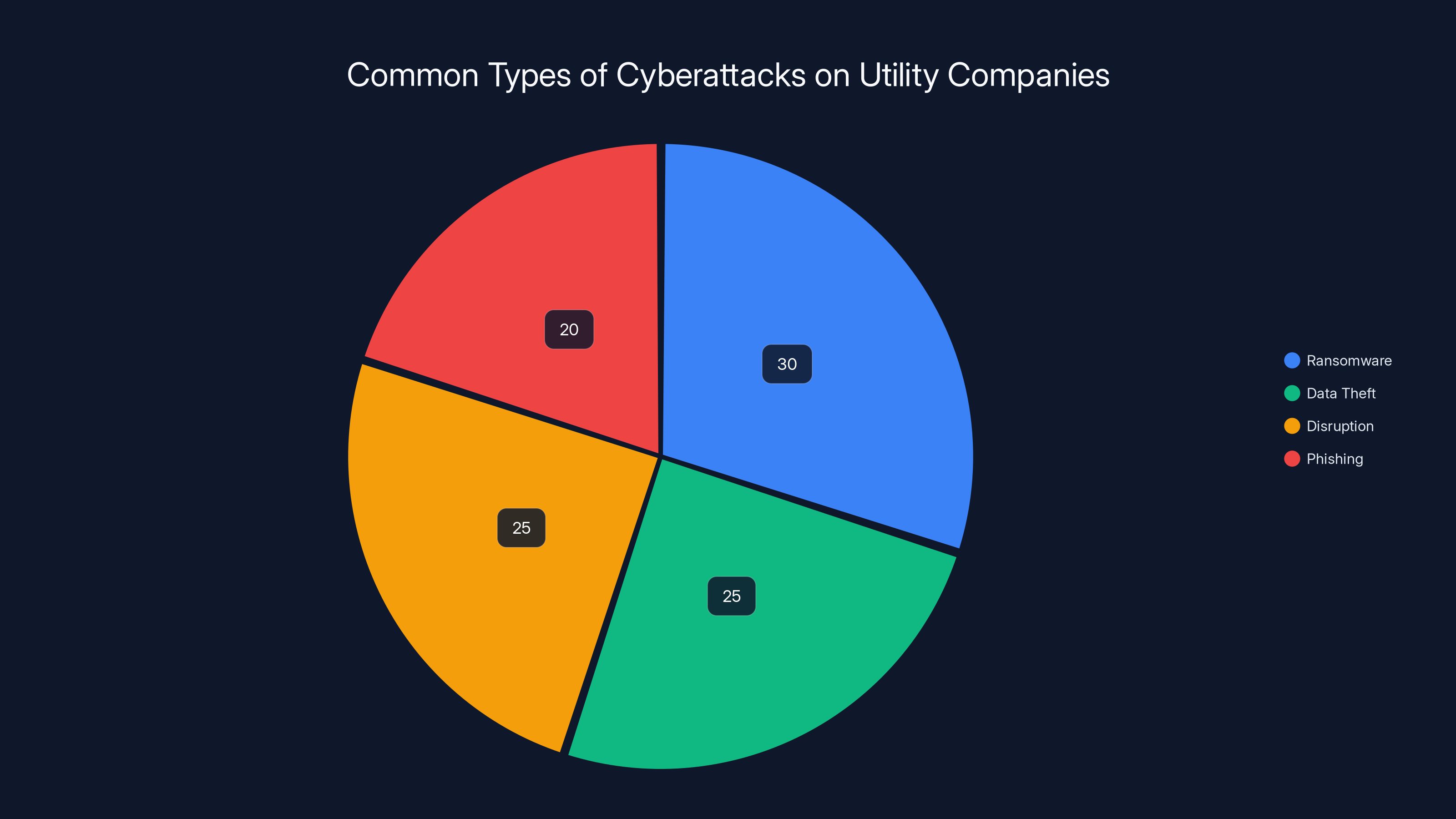
Ransomware and data theft are the most common cyberattacks on utility companies, each comprising around a quarter of incidents. Estimated data.
Cybersecurity Challenges in the Utility Sector
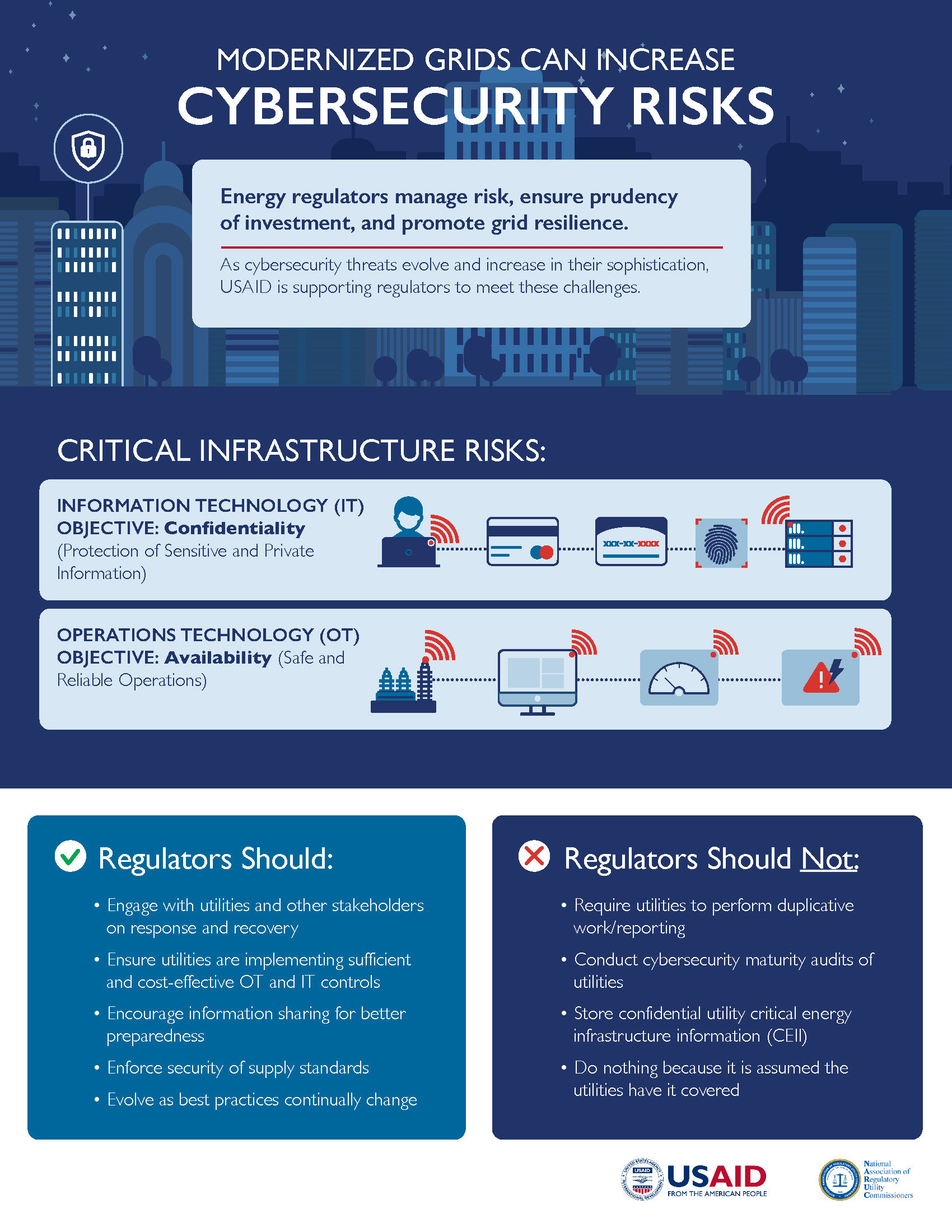
The utility sector, encompassing electricity, water, and gas services, is a prime target for cybercriminals. The interconnected nature of utility networks makes them vulnerable to attacks that can have cascading effects on critical infrastructure.
Common Threats
- Ransomware: Malicious software that encrypts data until a ransom is paid. Utilities are prime targets due to the critical nature of their services, as noted by HIPAA Journal.
- Phishing Attacks: Targeting employees to gain access to internal networks through deceptive emails.
- DDoS Attacks: Overloading systems with traffic to cause outages.
- Supply Chain Attacks: Compromising third-party vendors to infiltrate utility networks, as highlighted by Palo Alto Networks.
Security Best Practices
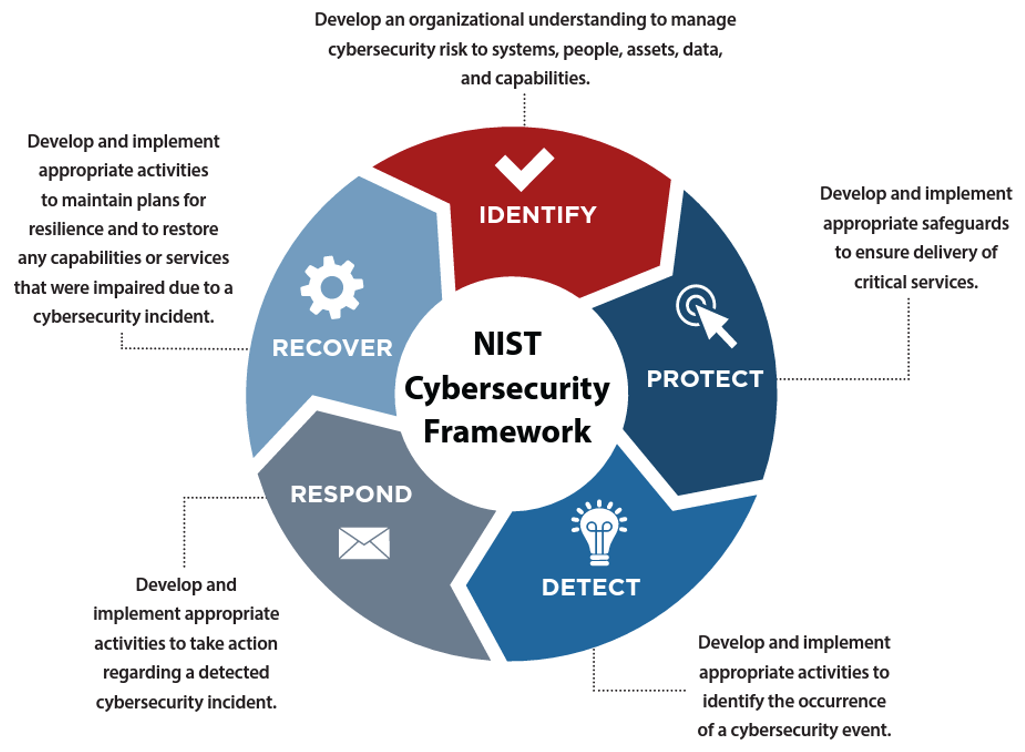
To mitigate these threats, utilities must adopt comprehensive security frameworks. This includes:
- Regular Security Audits: Identifying vulnerabilities and patching them promptly.
- Employee Training: Educating staff on recognizing and responding to phishing attempts.
- Network Segmentation: Isolating critical systems to prevent lateral movement by attackers.
- Incident Response Plans: Predefined strategies for quickly addressing breaches.
The Role of Technology in Enhancing Security
Advancements in technology offer new tools and strategies for bolstering cybersecurity in the utility sector. AI and machine learning, for example, are increasingly being used to detect and respond to threats in real-time, as discussed by Microsoft.
AI-Powered Solutions
AI can analyze vast amounts of data to identify patterns indicative of malicious activity. This allows for:
- Anomaly Detection: Identifying unusual patterns that could signal an attack.
- Automated Response: Quickly isolating affected systems to contain threats.
- Predictive Analytics: Anticipating potential vulnerabilities before they are exploited.

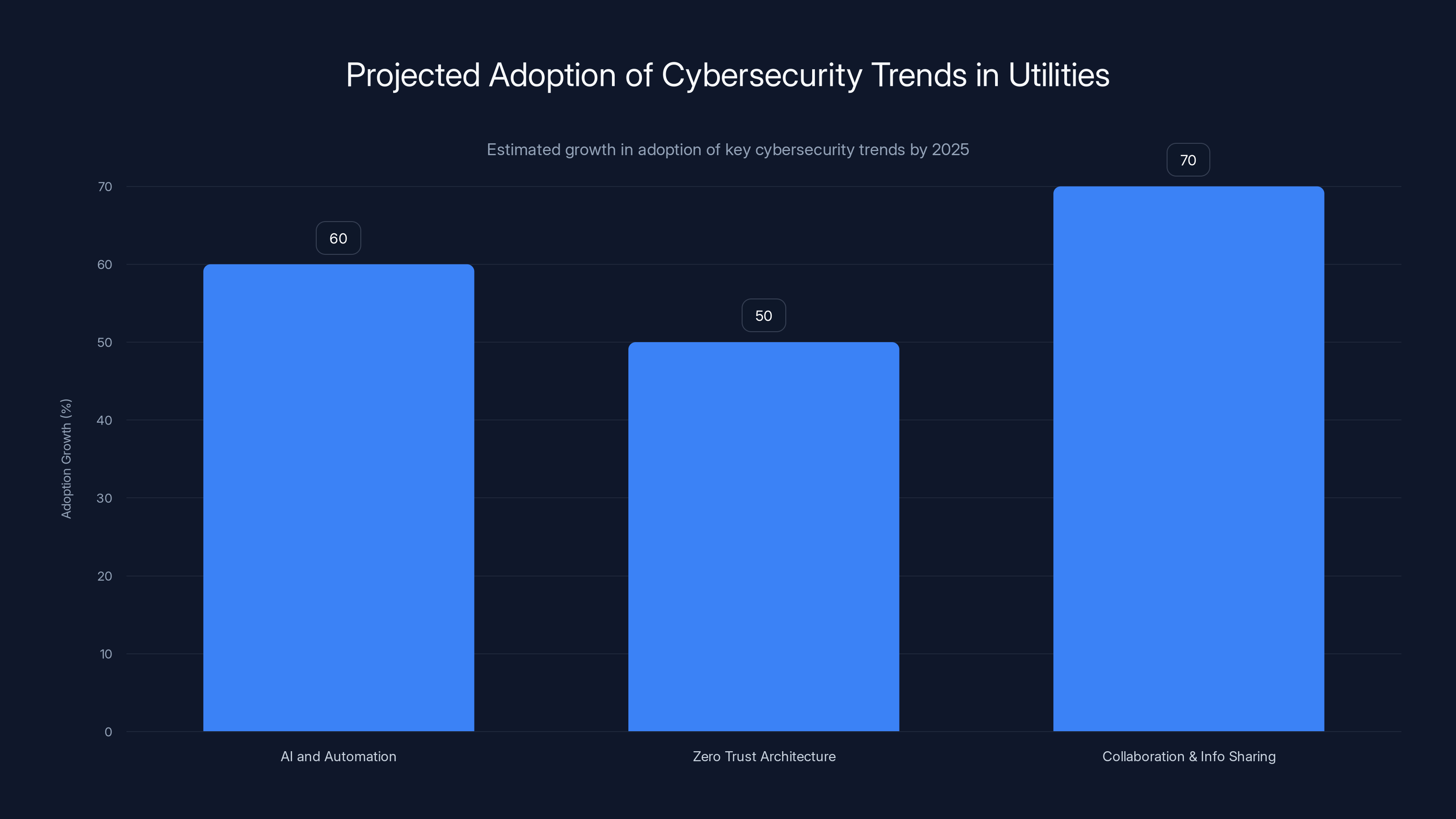
Estimated data suggests significant growth in the adoption of AI, Zero Trust, and collaboration in utility cybersecurity by 2025.
Implementing a Robust Cybersecurity Framework
Building a resilient cybersecurity infrastructure requires a multi-layered approach. Here’s a step-by-step guide to implementing best practices in utility cybersecurity:
- Risk Assessment: Conduct a thorough evaluation of potential threats and vulnerabilities.
- Policy Development: Establish clear security policies and procedures.
- Technology Deployment: Implement advanced security technologies such as firewalls, encryption, and intrusion detection systems.
- Continuous Monitoring: Use AI-driven tools to continuously monitor networks for suspicious activity.
- Incident Response Planning: Develop and routinely test incident response plans to ensure readiness.
- Regular Training: Provide ongoing cybersecurity training for employees to keep them informed about the latest threats and best practices.
Future Trends in Utility Cybersecurity
The landscape of cybersecurity is constantly evolving, with new threats and technologies emerging regularly. Here are some trends to watch in the utility sector:
Increased Focus on AI and Automation
The integration of AI and automation in cybersecurity is expected to grow, offering enhanced capabilities for threat detection and response, as projected by ITIF.
Emphasis on Zero Trust Architecture
Zero Trust models, which assume that threats could come from inside or outside the network, are gaining traction. This approach mandates strict identity verification for every person and device attempting to access resources on a network.
Collaboration and Information Sharing
Utility companies are increasingly collaborating with government agencies and other entities to share threat intelligence and best practices, as noted by ABC7 Chicago.

Common Pitfalls and How to Avoid Them
Despite the best efforts, certain pitfalls can undermine cybersecurity efforts. Here are some common mistakes and how to avoid them:
- Underestimating Insider Threats: Employees can inadvertently or maliciously compromise security. Regular training and monitoring can mitigate this risk.
- Neglecting Software Updates: Failing to apply software patches can leave systems vulnerable. Automating updates ensures timely application.
- Overlooking Third-Party Risks: Vendors and contractors can introduce vulnerabilities. Conduct regular security assessments of third parties.
Conclusion
The cyberattack on Itron serves as a timely reminder of the critical importance of cybersecurity in the utility sector. By understanding the nature of these threats and implementing advanced technologies and best practices, utility companies can better protect themselves against future attacks. As the threat landscape evolves, staying informed and prepared is key to safeguarding critical infrastructure.
FAQ
What is the Itron cyberattack?
The Itron cyberattack involved unauthorized access to the company's internal systems. However, according to initial reports, there was no tampering with sensitive data, and no significant disruption occurred, as confirmed by TechRadar.
How did Itron respond to the cyberattack?
Itron activated its cybersecurity response plan, which included isolating affected systems, conducting a forensic investigation, and enhancing security measures to prevent future intrusions, as detailed in InfoSecurity Magazine.
What are the common cybersecurity threats faced by utility companies?
Utility companies are susceptible to various threats including ransomware, phishing attacks, DDoS attacks, and supply chain attacks, as noted by Palo Alto Networks.
How can utility companies enhance their cybersecurity?
Utilities can enhance cybersecurity by conducting regular security audits, training employees, segmenting networks, and implementing incident response plans, as recommended by SC World.
What role does AI play in utility cybersecurity?
AI is used for anomaly detection, automated response, and predictive analytics, helping to identify and respond to threats in real-time, as discussed by Microsoft.
What are the future trends in utility cybersecurity?
Future trends include increased use of AI and automation, adoption of Zero Trust architecture, and enhanced collaboration and information sharing among industry players, as projected by ITIF.
What are common pitfalls in utility cybersecurity?
Common pitfalls include underestimating insider threats, neglecting software updates, and overlooking third-party risks, as highlighted by HIPAA Journal.
Key Takeaways
- Itron experienced a cyberattack affecting internal systems, as reported by SecurityWeek.
- Sensitive data was reportedly not compromised, as noted in StockTitan's filing.
- Itron's response involved activating a cybersecurity plan, as highlighted by InfoSecurity Magazine.
- AI and machine learning are key to future utility cybersecurity, as discussed by Microsoft.
- Zero Trust architecture is gaining traction in utilities, as projected by ITIF.
- Employee training and third-party assessments are critical, as noted by SC World.
Related Articles
- Understanding Data Breaches: Lessons from the Rituals Membership Database Breach [2025]
- Unveiling the Precursor: The Hidden Malware Before Stuxnet [2025]
- Inside the New Cyber Scam: How Hackers Exploit Microsoft Teams to Steal Your Data [2025]
- China-Nexus Cyber Actors Turning IoT Infrastructure into Botnets [2025]
- Anthropic’s Mythos Breach: Lessons Learned and Future Implications [2025]
- Discord Sleuths Gained Unauthorized Access to Anthropic’s Mythos | WIRED
![Understanding the Itron Cyberattack: Impacts and Lessons [2025]](https://tryrunable.com/blog/understanding-the-itron-cyberattack-impacts-and-lessons-2025/image-1-1777300587211.jpg)



