Duc Money Transfer Site Data Breach: A Comprehensive Guide [2025]
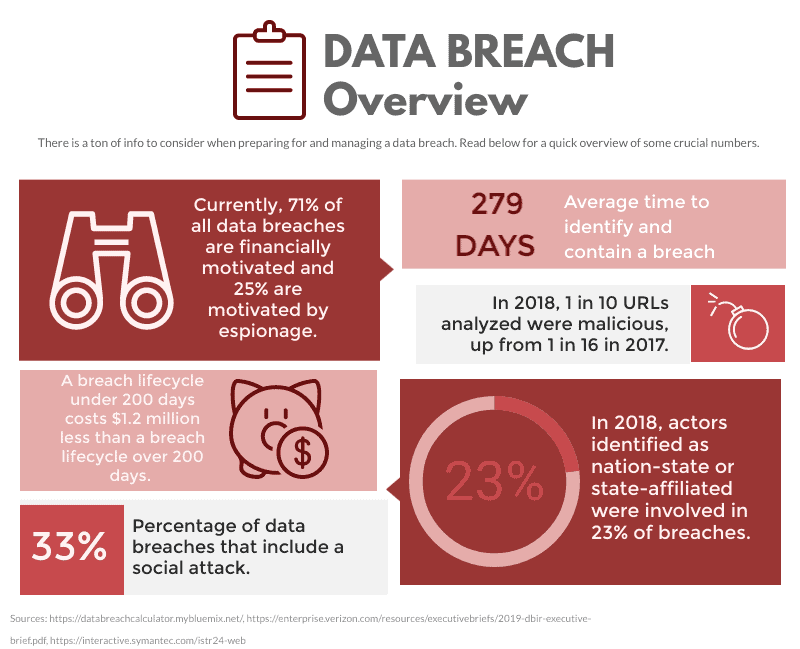
In an era where digital transactions are the norm, the safety of personal data has become a paramount concern. The recent incident involving Duc, a Canadian money transfer service, underscores the vulnerabilities that can arise from misconfigured databases. This article delves into the details of this breach, its implications, and offers insights into best practices for securing sensitive information.
TL; DR
- Breach Overview: Duc exposed 360,000 unencrypted customer files, including IDs and addresses, as reported by TechRadar.
- Security Flaw: Misconfigured databases led to the data leak, according to Silicon Canals.
- Impact: Potential identity theft and financial fraud risks for affected users, as highlighted by Digital Journal.
- Prevention: Implementing robust encryption and regular security audits, as advised by Palo Alto Networks.
- Future Outlook: Increased regulatory scrutiny and the need for enhanced cybersecurity measures, as discussed by Morgan Stanley.
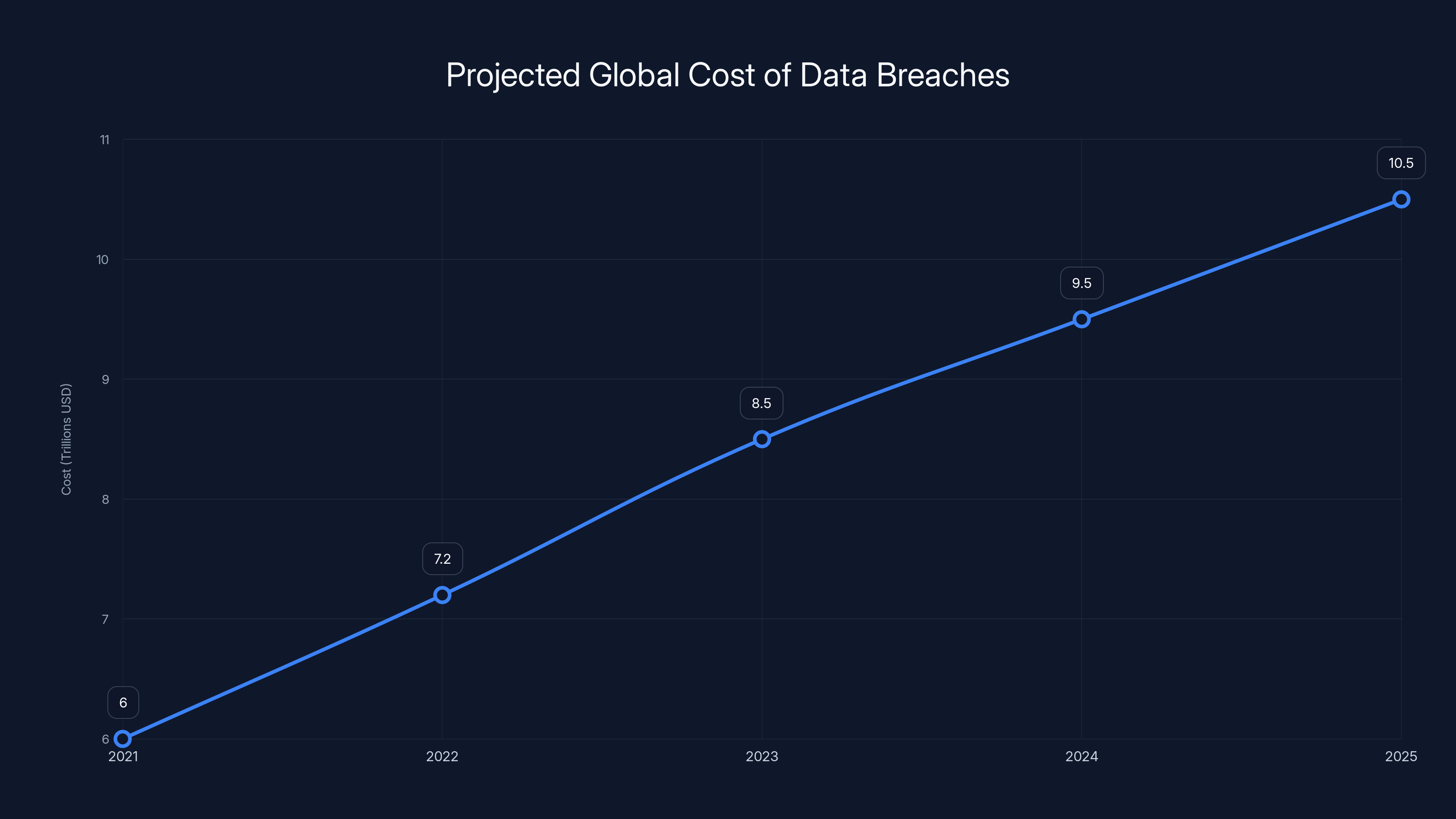
The global cost of data breaches is projected to rise significantly, reaching $10.5 trillion by 2025. Estimated data based on trends.
Introduction
In recent years, data breaches have become alarmingly frequent, with companies across various sectors falling prey to cybercriminals. The latest victim, Duc, a prominent money transfer platform, inadvertently exposed sensitive user data, including passports and driving licenses. This breach highlights the critical need for companies to prioritize data security and implement comprehensive protection measures.
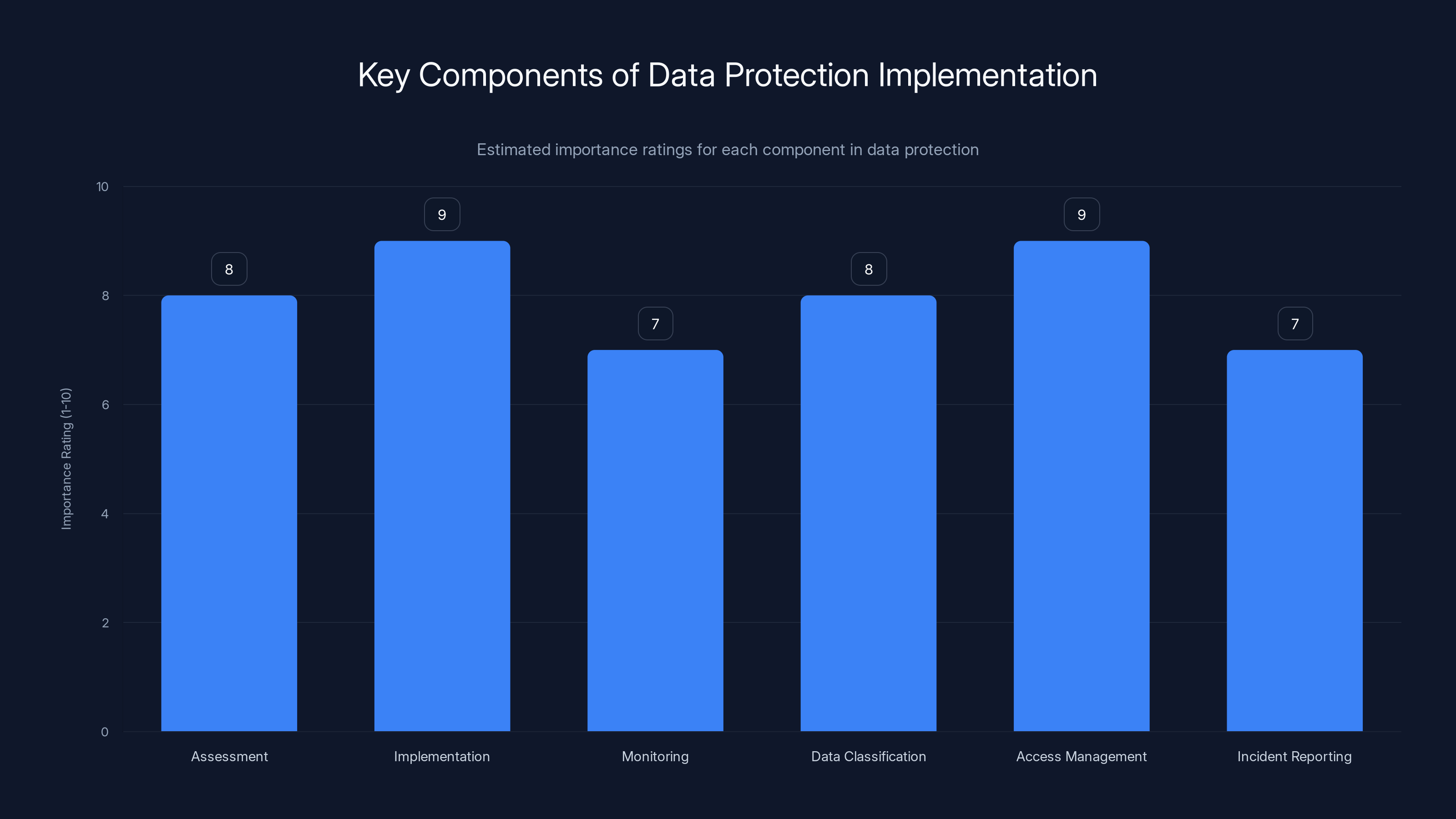
Implementation and access management are rated highest in importance for robust data protection. (Estimated data)
Understanding the Duc Data Breach
What Happened?
Duc, a leading money transfer service based in Canada, recently suffered a data breach, exposing sensitive information of 360,000 users. The breach was a result of a misconfigured database that left customer files accessible online without encryption. The exposed data included personal identification documents, addresses, and transaction details, as detailed by TechBuzz.
How Was the Breach Detected?
A security researcher discovered the vulnerability and promptly alerted Duc. Upon receiving the notification, the company secured the database to prevent further unauthorized access. However, the damage was already done, with significant amounts of personal data potentially compromised, as noted by Group-IB.
Data Affected by the Breach
The breach involved a wide range of sensitive information:
- Personal Identification Documents: Passports and driving licenses
- Contact Information: Addresses and phone numbers
- Transaction Details: Financial transactions history and account numbers

Implications of the Data Breach
Risks to Users
The exposure of personal identification documents poses significant risks to affected users. These risks include:
- Identity Theft: Cybercriminals can use stolen IDs to impersonate individuals and carry out fraudulent activities, as explained by NCOA.
- Financial Fraud: Access to transaction details can lead to unauthorized financial transactions and monetary loss, as reported by Data Protection Report.
- Privacy Violations: Users' personal information may be used for targeted phishing attacks, as highlighted by HIPAA Journal.
Legal and Regulatory Consequences
Data breaches often result in legal and regulatory repercussions for companies. Duc may face:
- Fines and Penalties: Non-compliance with data protection regulations can lead to substantial fines, as discussed by Fortune Business Insights.
- Loss of Trust: Customers may lose trust in the company's ability to safeguard their data.
- Litigation: Affected users might pursue legal action seeking compensation for damages.

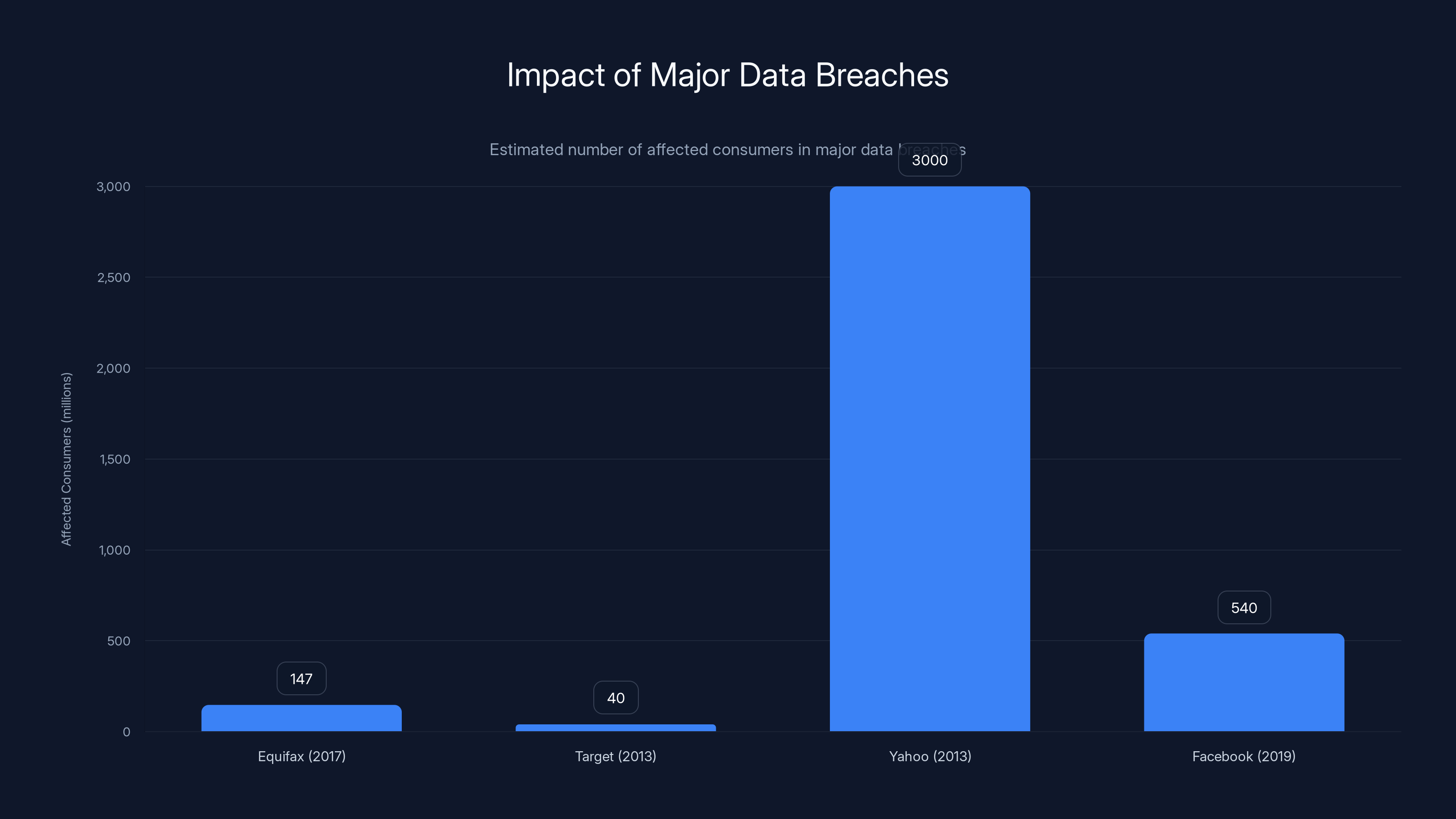
The Equifax breach affected 147 million consumers, highlighting the need for robust patch management and data minimization. Estimated data for comparison.
Best Practices for Data Security
Implementing Robust Encryption
Encryption is a critical component of data security, ensuring that sensitive information remains protected even if accessed by unauthorized parties. Companies should:
- Encrypt Data at Rest and in Transit: Use strong encryption algorithms to secure data stored in databases and during transmission.
- Regularly Update Encryption Protocols: Stay updated with the latest encryption standards to mitigate evolving threats.
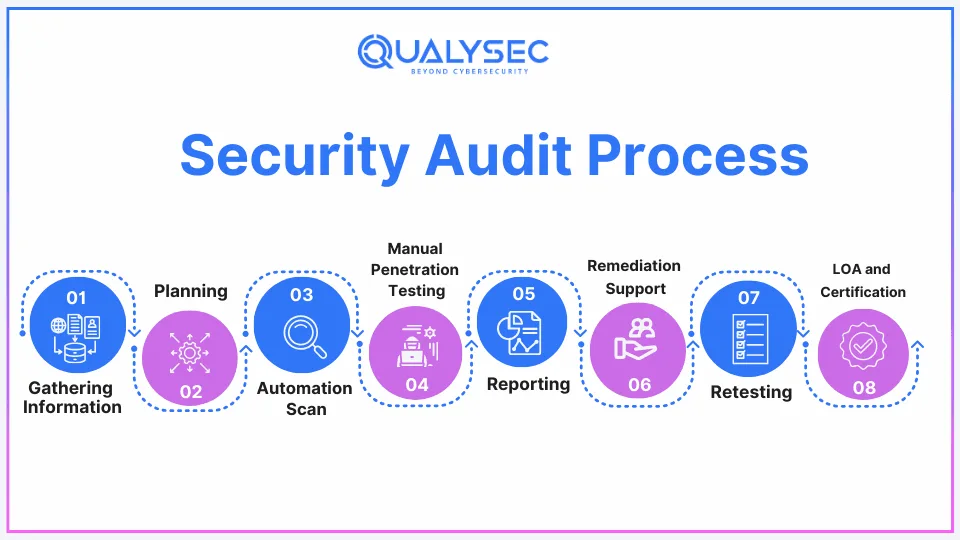
Conducting Regular Security Audits
Regular security audits help identify vulnerabilities and ensure compliance with data protection standards. Companies should:
- Perform Penetration Testing: Simulate cyberattacks to evaluate the effectiveness of security measures.
- Review Access Controls: Ensure that only authorized personnel have access to sensitive data.
Employee Training and Awareness
Human error is a common cause of data breaches. Training employees on data security best practices can significantly reduce risks:
- Phishing Awareness: Educate employees about recognizing and reporting phishing attempts.
- Secure Password Practices: Encourage the use of strong, unique passwords and multi-factor authentication.
Common Pitfalls in Data Security
Overreliance on Technology
While technology plays a crucial role in data security, it's not a silver bullet. Companies must also focus on:
- Human Factors: Implementing strict access controls and conducting regular training.
- Process Improvements: Developing comprehensive data management and incident response plans.
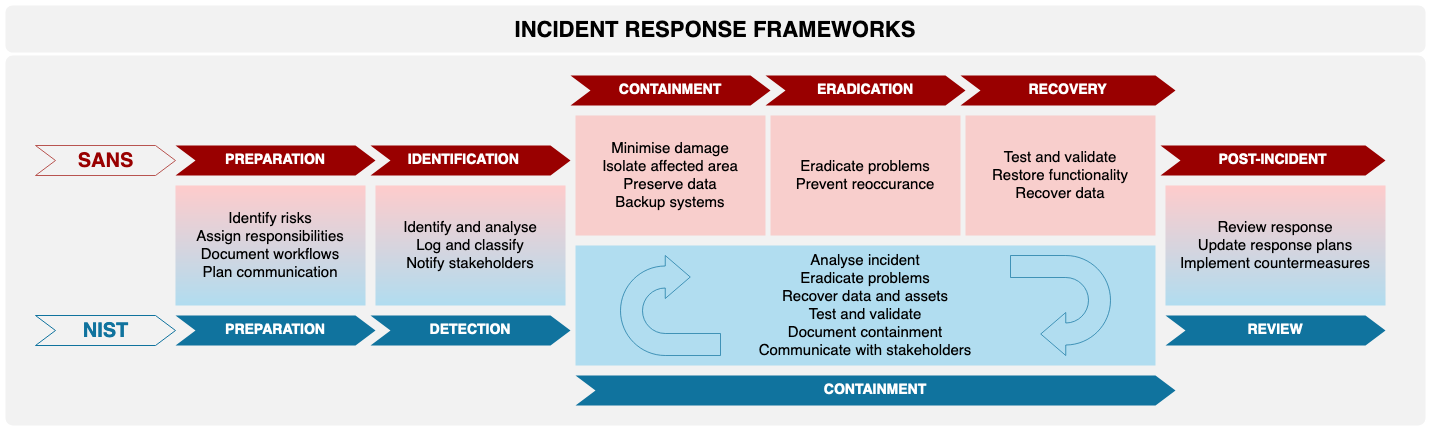
Inadequate Incident Response Plans
A well-defined incident response plan is essential for minimizing the impact of data breaches. Companies should:
- Define Roles and Responsibilities: Clearly outline the responsibilities of each team member during a data breach.
- Conduct Regular Drills: Simulate data breach scenarios to test the effectiveness of response plans.

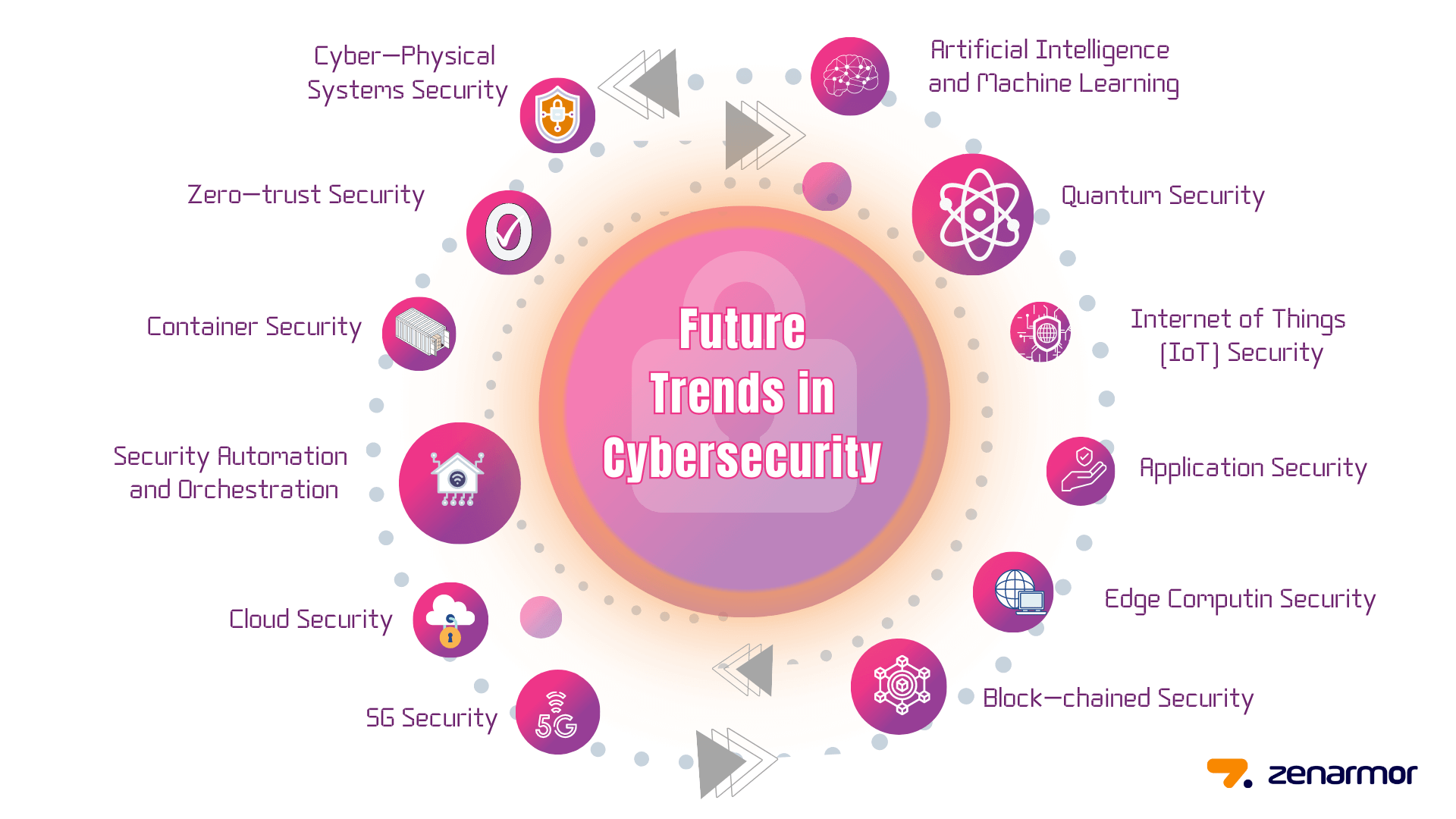
Future Trends in Data Security
Increased Regulatory Scrutiny
Governments worldwide are tightening data protection regulations to safeguard consumer information. Companies can expect:
- Stricter Compliance Requirements: Enhanced data protection standards and reporting obligations.
- Greater Accountability: Mandates for companies to demonstrate their commitment to data security.
Advancements in AI and Machine Learning
AI and machine learning technologies are revolutionizing data security by enabling:
- Anomaly Detection: Identifying unusual patterns that may indicate a data breach.
- Automated Threat Response: Responding to threats in real-time without human intervention.
Practical Implementation Guides
Setting Up Robust Data Protection Measures
Implementing effective data protection measures requires a multi-layered approach:
- Assessment: Conduct a thorough risk assessment to identify potential vulnerabilities.
- Implementation: Deploy a combination of encryption, access controls, and monitoring tools.
- Monitoring: Continuously monitor systems for suspicious activities and potential threats.
Developing a Comprehensive Security Policy
A well-defined security policy sets the foundation for effective data protection:
- Data Classification: Categorize data based on sensitivity and apply appropriate protection measures.
- Access Management: Implement role-based access controls to limit data access to authorized personnel.
- Incident Reporting: Establish clear procedures for reporting and responding to security incidents.
Case Studies: Learning from Past Breaches
Case Study 1: Equifax Data Breach
The Equifax data breach of 2017 exposed the personal information of 147 million consumers. Lessons learned include:
- Patch Management: Regularly update software to address known vulnerabilities.
- Data Minimization: Limit the collection of sensitive data to reduce exposure.
Case Study 2: Target Data Breach
In 2013, Target suffered a massive data breach due to compromised vendor credentials. Key takeaways include:
- Third-Party Risk Management: Assess and monitor the security practices of third-party vendors.
- Network Segmentation: Isolate sensitive data from other parts of the network to limit access.

Conclusion
The Duc data breach serves as a stark reminder of the importance of data security in today's digital landscape. Companies must adopt a proactive approach to protect sensitive information, leveraging advanced technologies and adhering to best practices. By learning from past breaches and implementing robust security measures, businesses can reduce risks and safeguard their customers' trust.
FAQ
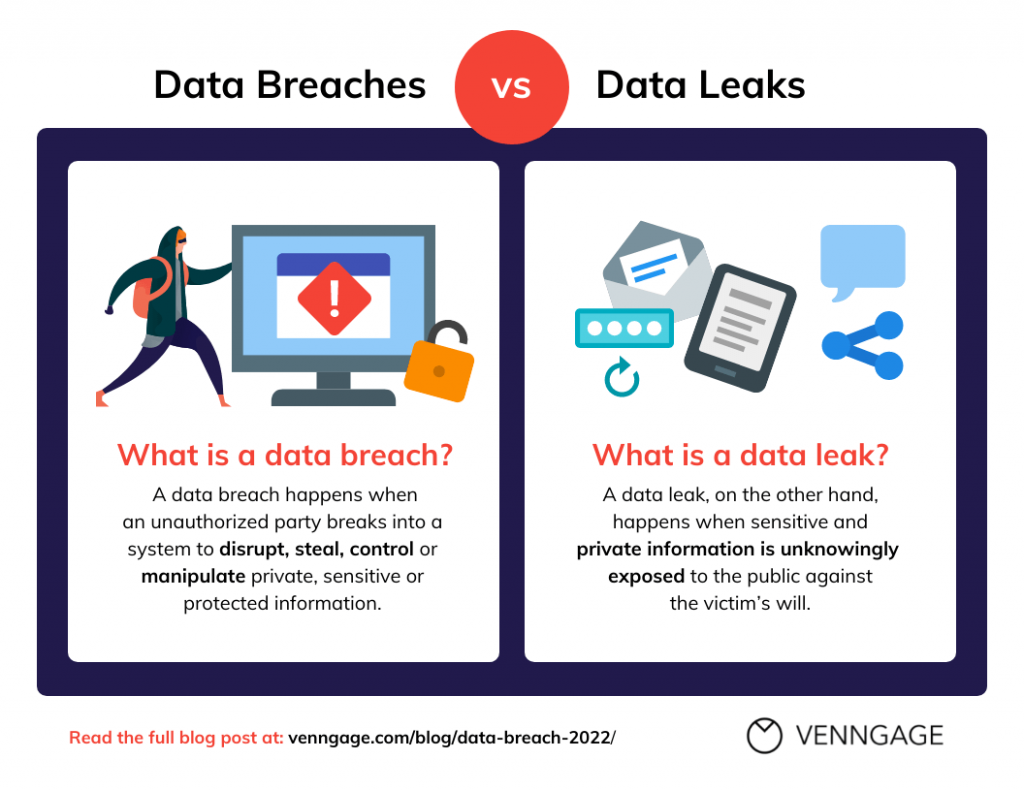
What is a data breach?
A data breach occurs when unauthorized individuals gain access to sensitive information, such as personal identification documents, financial records, or proprietary business data.
How can companies prevent data breaches?
Companies can prevent data breaches by implementing strong encryption, conducting regular security audits, training employees, and developing comprehensive incident response plans.
What are the consequences of a data breach?
Consequences of a data breach include financial losses, legal penalties, reputational damage, and loss of customer trust.
How do encryption and access controls protect data?
Encryption encodes data to make it unreadable without a decryption key, while access controls restrict data access to authorized personnel only.
What role do AI and machine learning play in data security?
AI and machine learning enhance data security by enabling real-time threat detection, automated response, and predictive analytics to identify potential vulnerabilities.
Why is third-party risk management important?
Third-party risk management is crucial because vendors and partners can introduce security vulnerabilities. Companies must assess and monitor their security practices to mitigate risks.
Key Takeaways
- Data breaches can expose sensitive information, leading to identity theft and financial fraud.
- Implementing robust encryption and access controls is crucial for data protection.
- Regular security audits and employee training can help prevent data breaches.
- AI and machine learning technologies are enhancing data security capabilities.
- Companies must adopt proactive measures to protect customer data and maintain trust.
Related Articles
- Hasbro Cyberattack: Lessons and Strategies for Cyber Resilience [2025]
- Safeguarding Older Apple Devices from DarkSword Attacks: A Comprehensive Guide [2025]
- Understanding Telehealth Security: Lessons from the Hims & Hers Data Breach [2025]
- The Hidden Risks of Exposed API Keys: How to Secure Your Cloud Systems [2025]
- Unraveling the EU Cyberattack: A Deep Dive into the Breach and Its Implications [2025]
- The Role of Spyware in Modern Law Enforcement: A Deep Dive into ICE's Use of Paragon's Tools [2025]
![Duc Money Transfer Site Data Breach: A Comprehensive Guide [2025]](https://tryrunable.com/blog/duc-money-transfer-site-data-breach-a-comprehensive-guide-20/image-1-1775226880626.jpg)



